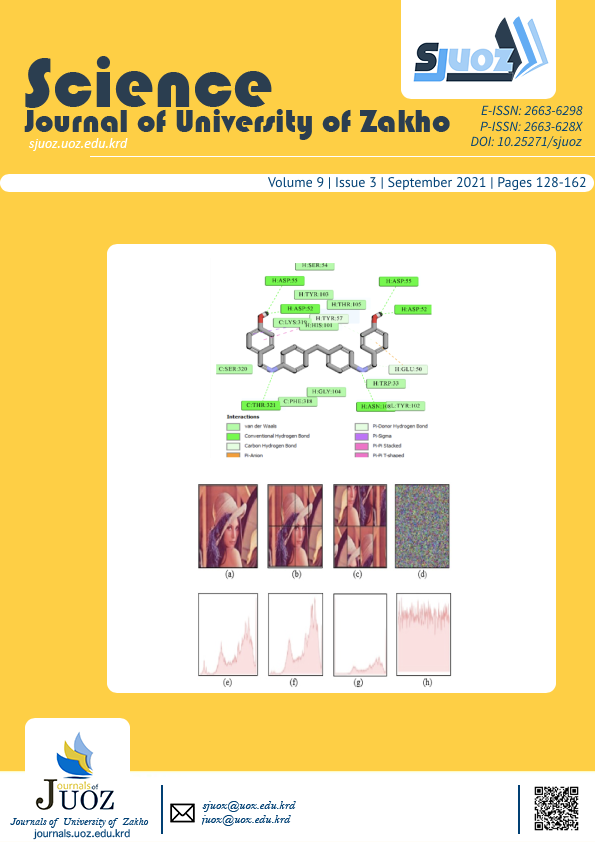
Color Image Encryption with a Novel Technique and Chaotic Singer Map
DOI:
https://doi.org/10.25271/sjuoz.2021.9.3.816Keywords:
Image, encryption, shuffling, chaotic, singer mapAbstract
One of the extreme efficient, important, and necessary means used to preserve the information and contents of the image through sending it over the Internet or network communication is image encryption. In this paper, a novel technology for images encryption has been proposed by using different methods. The proposed method consists of five stages. In the first stage, the original color image is divided into eight parts and shuffles it. The second stage separates the R, G, B matrix of the original image and then converts them into a binary code. Third stage generates secret keys by using singer map, where it can generate high pseudorandom sequences with high-speed performance. In the fourth stage, the logical XOR operator is applied to encrypt the image based on the three matrix and secret keys. Fifth stage is the process of decrypting which is the opposite of the encryption process. The suggested approach efficiency is validated via entropy, correlation, UACI and NPCR tests. Likewise, empirical outcomes and security test displayed that the proposed technology achieved secrecy and was capable of facing attacks and challenges.
Downloads
Downloads
Published
Issue
Section
License
Copyright (c) 2021 Araz B. Karim, Peshraw S. Abdalqader, Ziyad T. Najim, Abbas M. Salhd, Omar Y. Abdulhammed

This work is licensed under a Creative Commons Attribution 4.0 International License.
Authors who publish with this journal agree to the following terms:
- Authors retain copyright and grant the journal right of first publication with the work simultaneously licensed under a Creative Commons Attribution License [CC BY-NC-SA 4.0] that allows others to share the work with an acknowledgment of the work's authorship and initial publication in this journal.
- Authors are able to enter into separate, additional contractual arrangements for the non-exclusive distribution of the journal's published version of the work, with an acknowledgment of its initial publication in this journal.
- Authors are permitted and encouraged to post their work online.